Many HEXUS users are likely to own a Western Digital MyCloud NAS device. These are popular entry-level and up network storage devices but recently an "easy" authentication bypass vulnerability has been unveiled. Keeping their personal/family/business data private will be a major concern for many users of NAS devices, but reportedly WD has done nothing to patch the flaw to which it was alerted over a year ago.

'Welcome' to anyone
After alerting WD to the privilege escalation bug in April 2017, security researcher Remco Vermeulen said that WD stopped responding to his communications. It is common practice for 'white hat hackers' to give companies 90 days to respond but Vermulen went gone way beyond this timescale (260 days) giving WD plenty of chance to respond and patch. He found that WD had issued firmware fixes over the last year, but none of them fixed this easy to exploit remote access flaw. Meanwhile, the bug was independently found by another security team, which released its own exploit code, reports TechCrunch.
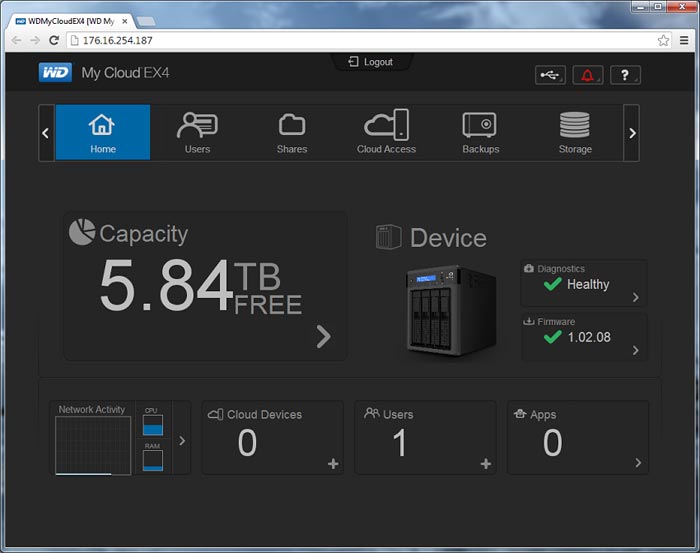
The remote access bug is "easy" to exploit, according to Vermulen. If your MyCloud device is set to allow remote access over the internet, an unauthenticated user can create a valid session if the username=admin cookie is set. After that the new user has "complete control" over the user's data via the MyCloud web interface. The reason for this weakness in security is that the web-based dashboard "doesn't properly check a user's credentials before giving a possible attacker access to tools that should require higher levels of access" explains the source report.
Despite apparently ignoring Vermulen, a WD spokesperson responded to TechCrunch's query about this privilege escalation flaw. "We are in the process of finalizing a scheduled firmware update that will resolve the reported issue," said the company official. With regard to timing, the patch will arrive "within a few weeks". WD admitted that My Cloud EX2, EX4 and Mirror products were vulnerable, but not the newer My Cloud Home devices.

If you own one of the affected WD products then Vermeulen recommends that users "just disconnect" the device for now, to be sure to keep their data safe.













