Microsoft has published a new web based tool which has the stated aim of "Preventing weak passwords by reading your mind". The new tool is snappily called Telepathwords and was built by researchers from Microsoft Research (MSR) and a Carnegie Mellon University PhD student intern.
Telepathwords works by utilising the knowledge and data Microsoft has of common passwords, such as those made public from past security breaches. Also common phrases and searches on the web are considered as are other password choosing behaviours such as typing keys from your keyboard due to their position; like qazwsx or, heaven forbid, 123456.
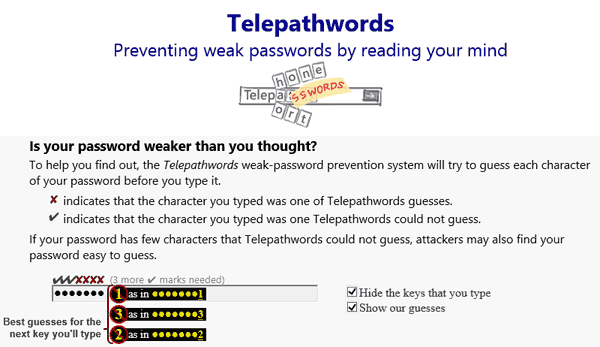
the X marks a successful prediction
Microsoft's 'prediction engine' uses a very large database of words so it's not sent to your computer when you use Telepathwords. However the passwords you type and test are not logged by Microsoft but it does record data of "mouse movements and the timings of when characters are added to or removed from your password," for its research into understanding how users choose passwords. This log is encrypted before being sent to Microsoft.
While the researchers are pretty proud of the Telepathwords tool they are the first to admit that it can't prevent all weak passwords. For instance the researchers suggest that an attacker might know some of your personal information from some other source, which makes your password more guessable to them.
I've given Telepathwords a test drive and it cottoned onto a very old password I used to use pretty quickly. I also got the warning about 'profanity' pop up, as shown below, though my password didn't contain any such word...