Security research and solutions outfit Eclypsium has published an interesting report highlighting insecure device driver packages from major PC components makers. By their very nature, drivers have deep access to PC systems and if they have vulnerabilities they can become powerful tools for attackers to "escalate privileges and persist invisibly on the host". Unfortunately, it seems that the problem of insecure drivers is widespread and Eclypsium found that "more than 40 drivers from at least 20 different vendors," suffered from security flaws.
Eclypsium's report is catchily, and appropriately, titled 'Screwed Drivers'. Worryingly, the report names the blue, red, and green team's (Intel, AMD and Nvidia) drivers among its hall of insecure shame, as well as stating that "every major BIOS vendor," is providing insecure drivers to its customers. Moreover, "all the vulnerable drivers we discovered have been certified by Microsoft," so such certifications aren't any reassurance, in case you thought they might be.
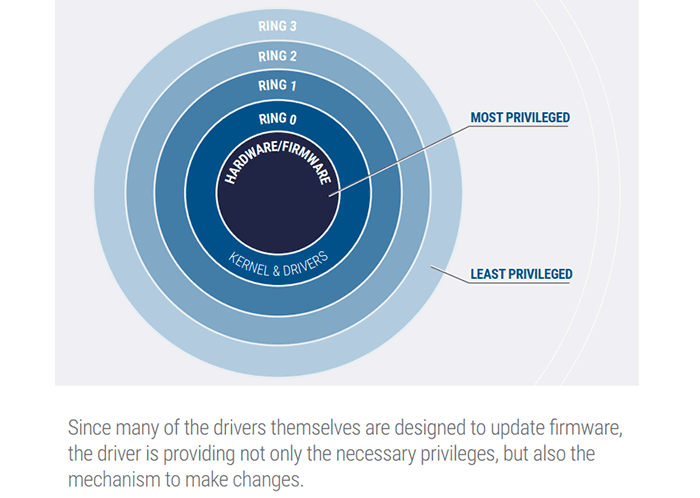
The report goes on to highlight that drivers can allow highly privileged access, moving an attacker far beyond administrator level privileges (see chart, above). Malware running in this space could be used to gain full control over the system and potentially the underlying firmware. Even after being conventionally 'wiped' these systems, if sold on and re-used, could continue to be used for attacks or data gathering.
It is noted that escalation of privileges needs a vulnerable driver to be already on the system, as installed by an admin. However, as the report highlights, there are plenty of flawed drivers out there and you might be running a PC which uses one.
Eclypsium says that we are often told to update drivers and firmware to stay secure but "the very drivers and tools that would be used to update the firmware are themselves vulnerable and provide a potential avenue for attack". Nevertheless, the security firm encourages users and organisations to continuously scan for outdated firmware, and update to the latest version of device drivers when fixes become available from device manufacturers.
We don't have much in the way of detail about vulnerability specifics as some details are wisely under embargo and they want fixes available for customers before the general public can look more closely at these flaws.
List of affected vendors:
- ASRock
- ASUSTeK Computer
- ATI Technologies (AMD)
- Biostar
- EVGA
- Getac
- Gigabyte
- Huawei
- Insyde
- Intel
- Micro-Star International (MSI)
- Nvidia
- Phoenix Technologies
- Realtek Semiconductor
- SuperMicro
- Toshiba
Eclypsium has made both the Screwed Drivers report and its Def Con presentation covering the report available to download (both PDFs).













