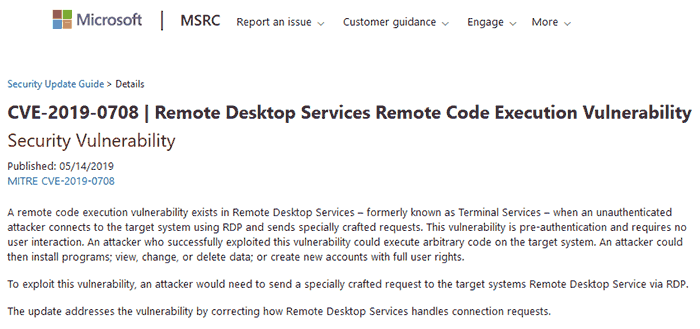
In efforts to prevent another WannaCry (2017) style malware outbreak, Microsoft has released some software patches for older Windows systems, including some that are long past their support dates. The CVE-2019-0708 patches that are available target a critical Remote Code Execution vulnerability in Remote Desktop Services (formerly known as Terminal Services), to prevent worm transmission. Such transmission would be pre-authorised and require no user interaction on an unpatched system. At the time of writing Microsoft has not observed any exploitation of this vulnerability but thinks it is "highly likely that malicious actors will write an exploit for this vulnerability and incorporate it into their malware," in the future.
Windows versions that are affected
Microsoft notes that vulnerable in-support systems include Windows 7, Windows Server 2008 R2, and Windows Server 2008 systems. For such systems you can download updates via the Microsoft Security Update Guide or they will be delivered via automatic updates, if enabled.
Windows XP and Windows 2003 systems are out of support, and being so aged Microsoft strongly recommends users update to a newer OS. However, it has made fixes available for these systems as patch KB4500705.
Lastly, customers running Windows 8 or Windows 10 are not affected by the critical Remote Code Execution vulnerability outlined in the intro. Microsoft crows that "it is no coincidence that later versions of Windows are unaffected". It explains "Microsoft invests heavily in strengthening the security of its products, often through major architectural improvements that are not possible to backport to earlier versions of Windows."
Microsoft mentions that some older Windows OSes will have partial mitigation against the vulnerability if they have Network Level Authentication (NLA) enabled, as NLA requires authentication before the vulnerability can be triggered. However, affected systems are still vulnerable to Remote Code Execution (RCE) exploitation if any attacker somehow has valid credentials.
Just because updates are available doesn't mean they will be applied
WannaCry / Wanna Decryptor had a devastating impact on PCs worldwide, famously including systems installed in the UK's health services. However, the issuing of these patches for older OSes doesn't mean that users, companies and institutions will get around to updating their old systems anytime soon.













