Google has increased the scope of its Safe Browsing API to protect users from deceptive malware and phishing attacks. In particular it has targeted the commonly seen fake download buttons, and similar. A Google Online Security blog post, published earlier this week, asserts that the move will help create a world wide web with "No More Deceptive Download Buttons".
If Google has detected a site which deploys/contains a deceptive download button, or an image ad that falsely claims your system is out of date, for example, the site will be flagged. Any person using a browser which uses Google's Safe Browsing API (which includes Chrome, Firefox, and Safari) will be warned of what is to come next, with the option to read more about the risk and/or go 'back to safety'.
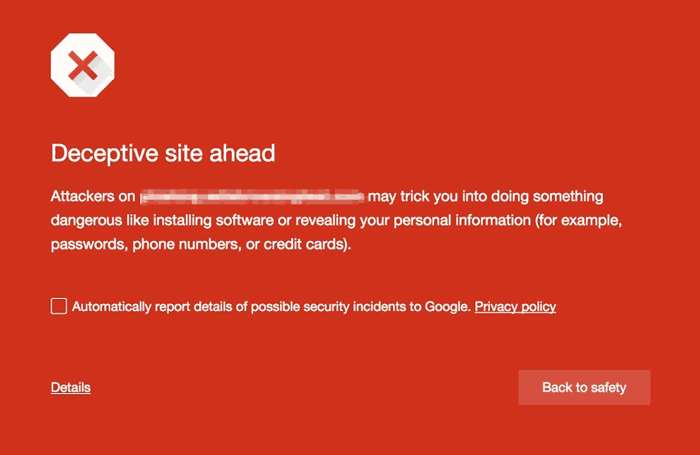
Such deceptive buttons are categorised as 'social engineering attacks'. Sometimes they aren't hosted by the site directly however, they might be contained in ads on the site. However the whole site will be flagged as shown above if Google detects that elements on the web page either:
- Pretend to act, or look and feel, like a trusted entity — like your own device or browser, or the website itself.
- Try to trick you into doing something you'd only do for a trusted entity — like sharing a password or calling tech support.
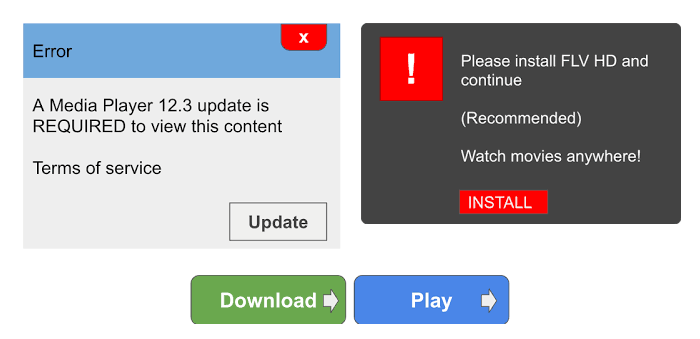
Three deceptive website element examples, soliciting your clicks
Google provided some images, reproduced above, which are examples of the kinds of buttons/interactions the Safe Browsing API will detect and block.
If you host a site you might have completely innocently had such buttons embedded in your site by an advertising partner, or your site might have been hacked, for example. Google recognises this and will notify webmasters of such site problems and watch for them to be 'cleaned up'. Part of the Safe Browsing algorithm will measure the website cleanup time and re-infection rate.













