There is a new security focussed feature being developed for Firefox 14 called ‘Click to Play’. The idea is to block the default loading of plugins like Flash, Java and the PDF viewer that are often used as routes to run auto-loading/running drive-by exploits via the web browser. I actually have experience of receiving such a payload via a Flash banner ad which downloaded a trojan to my old netbook. I think the ad was served by Clicksor, well known for malware infested adverts. Similarly the security bods at Sophos have experience of drive-by downloading of booby trapped PDFs.
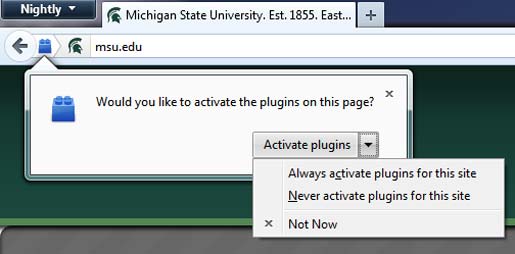
With the new Firefox Click to Play feature, when a page you have opened has a plugin that wants to load content, it will wait for you to click to confirm that you are happy for it to load (i.e. to opt-in). For example, in YouTube, the first time you visit the site with the Click to Play browser, the space where the video would be is replaced by the plugin icon, which you click to start the Flash that loads the video player and streaming video.

Benefits of Click to Play
- Better security - default deny
- Lower memory usage
- Lower CPU usage (might save you some battery if you are on the road)
- Your preferences for each site/domain can be saved AKA site specific permissions
There are various plugins for Firefox which have similar functionality; NoScript, Flashblock and ScriptNo stop various java and flash embedded files from running/loading automatically. The popularity of these plugins with tech savvy Firefox users probably flagged up to the Firefox developers that it is probably a good feature for the main program. The people who need protecting the most from these drive-by exploits might never download or know about script blocking extensions. For the average punter it won’t take long to white list their favourite trusted web sites and be enjoying quite a bit more security when they browse further afield (default deny).













