Earlier this week the news about the Heartbleed bug broke and since that time web users have been told all sorts of things about the dangers and what they should and should not do. There's been conflicting advice, particularly about changing your passwords, doing the rounds so it's been difficult to know what to do, if anything.
In summary Heartbleed is a bug in the popular web encryption program OpenSSL which has been used by hackers to grab data which could contain sensitive info such as passwords, PINs and so on. The issue has apparently been open to exploitation for about two years until it was brought to light earlier this week.
Reuters reports that OpenSSL is used on about two thirds of all web servers and some software programs have OpenSSL code built into them. OpenSSL has now been patched by the developers but we must wait for websites and programs to be updated with the software before we know it's safe to change our passwords.
Big name web companies such as Google, Facebook, Amazon and Yahoo have all already taken steps to patch their OpenSSL using services. However with the average web user using so many sign-on services day to day it's difficult to keep track of which ones have updated (list via Mashable) so you can change your password and which ones haven't acted as yet.
Kaspersky wrote to HEXUS today to inform us of a couple of resources which may help confused web users. It provided a couple of resources for you to check to first see if the sites you use were vulnerable and secondly to see if it is still vulnerable. It's also detailed the steps in a blog post.
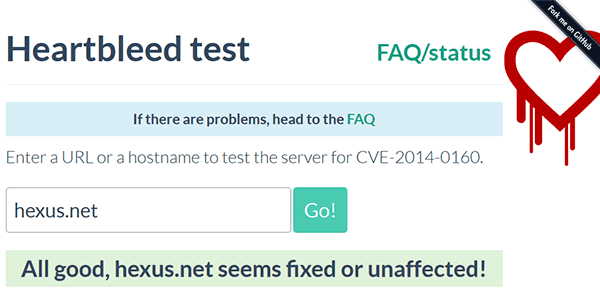
In brief; you can check from a long list of websites which were vulnerable here. Then you can check if the vulnerability remains by inputting the base URL at the Heartbleed test page. If the vulnerability was present before but is already fixed then it's a good time to update your password. If it's still not fixed it's probably worth waiting as the site isn't secure yet.













