Researchers at the KU Leuven University in Belgium have devised a way to open and drive away a Tesla Model S in seconds - without owning a genuine Tesla key fob. Using approx $600 of off-the-shelf parts, including a couple of radio sensors and a Raspberry Pi, you can see a researcher swiftly hacking a parked up and charging Tesla S and then driving casually away. Importantly, this proof of concept hack method was shared with Tesla a year ago, and the June 2018 encryption system update fixes this (with new key fob hardware) and adds an optional PIN code entry system once you get into the car.
The video above shows the hacking methodology off very succinctly and is worth a watch. While the 'hacker' walks near to the car owner to clone the key fob with his equipment this could also easily be done if the Tesla owner leaves his keys near the front door or similar.
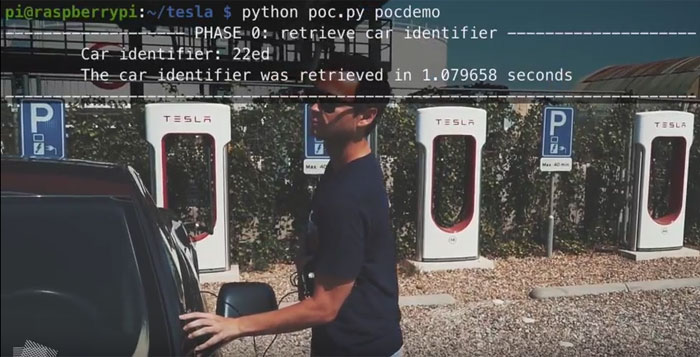
According to the researchers the Achilles heel of the Tesla keyless entry system was the fobs -manufactured by Pektron - only use 40-bit ciphers to encrypt messages and send their lock/unlock codes. The researchers computed all possible key combinations and stored them in a 6TB lookup table. Once the codes were cloned from a fob they could scan nearby (in owners pocket in video) the $600 electronics gadget only required 1.6 seconds to spoof a working key.
According to Tesla, Model S cars sold since June 2018 aren't vulnerable to this attack, due to upgraded key fob encryption that it implemented in response to the KU Leuven research. Also in June Tesla updated its anti-theft software to allow for a PIN to be entered by the driver to drive the car. Owners of older Tesla S models can pay for updated key fobs and/or turn on the PIN to protect against this hacking method. Tesla paid the KU Leuven team a $10,000 'bug bounty' for their work.

Of course Tesla isn't the only car maker affected by these kinds of key fob cloning attacks, or similar tech hacks like 'relay attacks'. Other Pektron-based entry systems that might be vulnerable to this particular hacking method are employed by in cars sold by McLaren and Karma and motorcycles sold by Triumph. If unsure about you vehicle's vulnerability to key fob hacks and cloning some vendors recommend 'signal-blocking pouches' that block radio communications to key fobs when they are not in use.