Researchers at Erlangen University have demonstrated that they can breach Android security with the help of a fridge-freezer. The scientists have developed a recovery tool called FROST which stands for Forensic Recovery of Scrambled Telephones. They found that they could unlock an Android smartphone’s sensitive data by retrieving disk encryption keys from RAM following a “cold” boot. Also a lot of other info was available in the Ram dump.

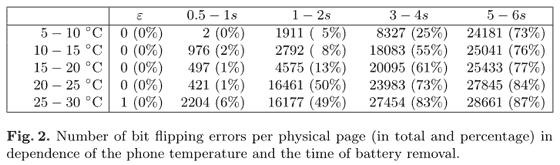
Conditions for a successful memory rip
So far the scientists have had success with the Samsung Galaxy Nexus. They chose this smartphone as it is a standard “official” Google phone, with a version of Android unmodified by the manufacturer. The Galaxy Nexus was the first device with Android 4.0, which added encryption support. PIN protection and storage disk encryption are no barrier to the FROST method however the phone must have an unlocked bootloader for the method to work.
The method
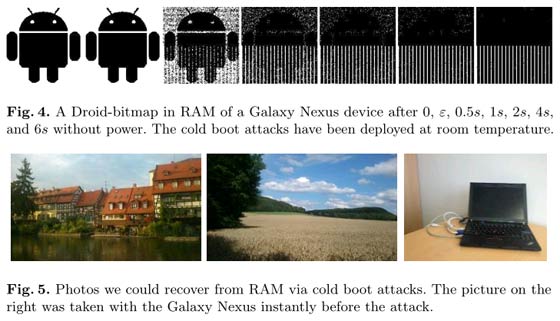
The smartphone is chilled down to about -15 degrees Celsius for an hour. The cooling of the phone lets the RAM contents persist for much longer. With the phone powered on the scientists pull the battery out – so the OS can’t go through normal shutdown procedures – and then the battery is re-inserted and phone powered back on as quickly as possible. Now the fastboot mode is invoked and FROST run from the recovery menu. The phone was connected to a PC and the phone’s memory dumped copied over for poking through at leisure. The scientists could sift through the data and recover images, emails, browsing history and also AES keys (using a modified version of AESKeyFind).
It’s an interesting experiment and reminds me a lot of when I used to use reset-resident memory ripping programs on the old 16-bit computers (Amiga or Atari) to rip and save graphics and sound modules from RAM. Also, some time in the past, I remember hearing of people using a deep freeze to unlock car stereo systems, resetting the PIN to 0000. When if first saw the headlines for this FROST smartphone method I thought it may be more akin to the car stereo method than Amiga RAM ripping.
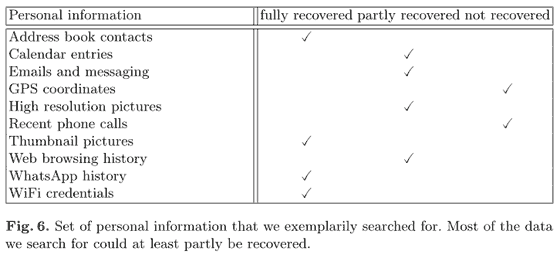
Is FROST something to be concerned about, if a villain gets hold of your smartphone? It’s probably something else to worry about - if you did bother to use a PIN password and had encrypted your data but left your bootloader unlocked after reflashing your droid. At this time the whole procedure seems quite a lot of effort for its possible returns.













